If you cannot access, inspect, or replace a core part of your own operation, you are exposed.
That exposure does not always look dramatic. Sometimes it looks like delay, uncertainty, excuses, friction, invoices, or silence. But the effect is the same: your momentum is no longer fully yours.
The hostage pattern is older than websites
People often think technical captivity is a modern web problem, but the underlying pattern is much older. A business becomes vulnerable whenever a critical asset is concentrated in someone else’s hands without clarity, redundancy, or accountability.
In one era it may be printing plates, artwork, layout files, customer lists, publishing rights, molds, specifications, or machinery settings. In another era it may be hosting accounts, domain access, code repositories, API configurations, design source files, analytics accounts, or cloud dashboards. The shape changes. The lesson does not.
Dependency becomes dangerous the moment it turns opaque.
Trust is not the problem. Unclear control is the problem.
How hostage situations usually begin
They rarely begin with obvious malice. They begin with convenience. Someone is hired to handle a task. They know the tools. They promise speed. They set things up quickly. The business is busy, grateful, and relieved to move on. Documentation is postponed. File organization is postponed. Ownership boundaries are blurred. Passwords stay with one person. Systems are explained verbally rather than structurally.
Then one day, a change is needed. A small update becomes a negotiation. A simple request becomes a delay. A missing file becomes leverage. A vanished contact becomes a crisis. A locked account becomes a lesson.
The hostage moment often appears only after the system is already critical.
By the time you feel trapped, the dependency has usually been there for much longer than you realized.
The emotional cost is real
Business hostage situations are not only operational problems. They affect confidence. Once an owner feels they cannot safely touch their own systems, hesitation creeps in. Requests get delayed. Experiments stop. Improvements shrink. The site or system begins to feel like dangerous territory rather than usable property.
That feeling is one of the most corrosive forms of dependency because it trains passivity. It teaches the owner to wait, to avoid, to outsource by reflex, and to fear the very infrastructure they pay to maintain.

What “held hostage” really means
It does not always mean someone is literally demanding money, although that can happen. More often it means the business is unable to act freely because key functions are bottlenecked by someone else’s control.
A hostage condition can mean:
- you cannot obtain your own source files
- you do not know where the current versions live
- you do not control the domain or hosting credentials
- you cannot make a simple content change without waiting
- you do not know how the system is structured
- you are paying to preserve ignorance rather than capability
The website is where many businesses feel this first
Websites are a common place for this lesson because they sit at the intersection of branding, operations, lead generation, reputation, publishing, and technical management. A site is rarely “just a site.” It is often the public surface of the business itself.
When a business owner cannot access files, edit pages, replace assets, or even understand the site tree, they are not simply missing a convenience. They are separated from a major organ of the business.
If a contractor vanished tomorrow, could you still locate, understand, and continue your site?
If the answer is no, then the problem is not hypothetical.
Why website.co.jp takes this so seriously
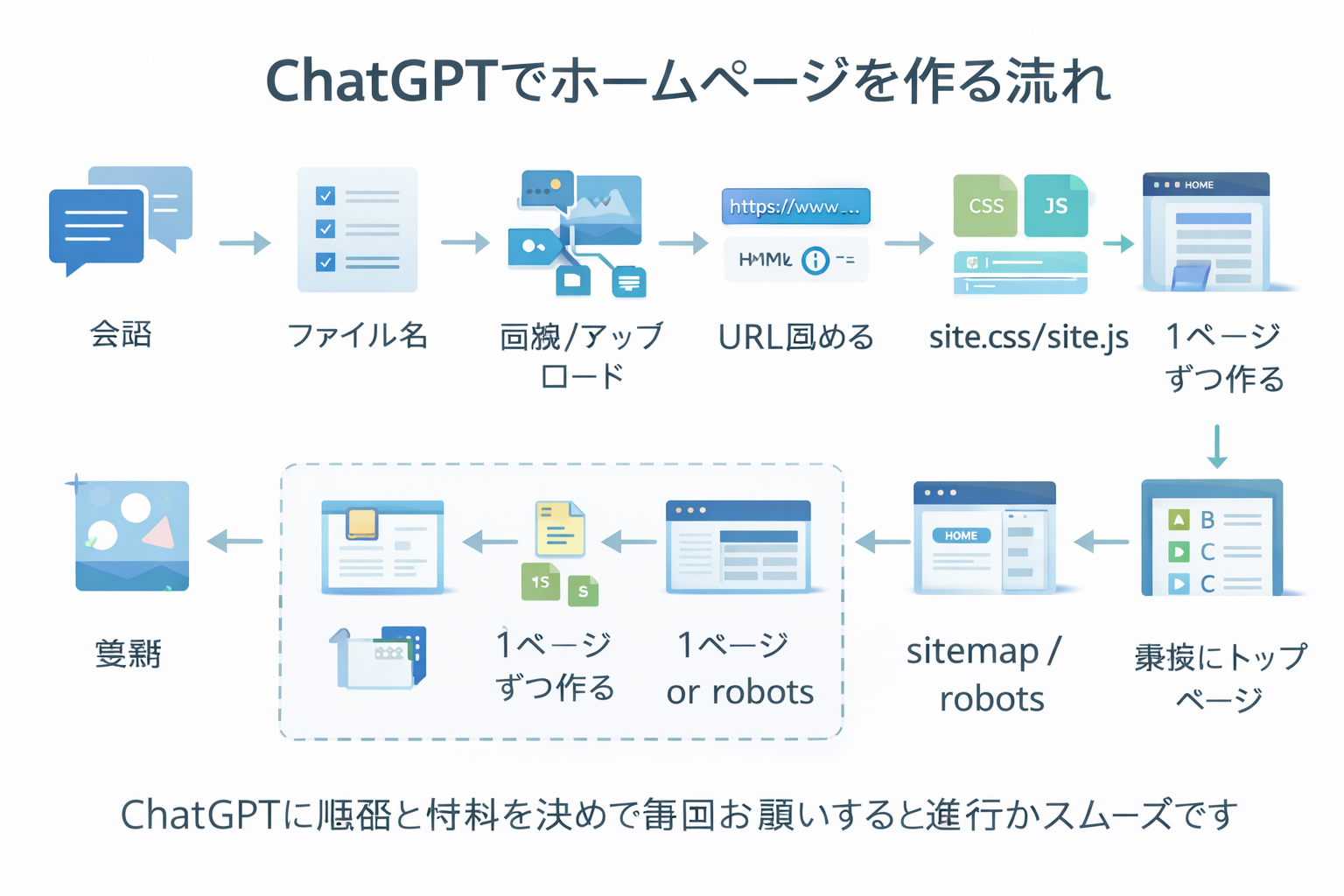
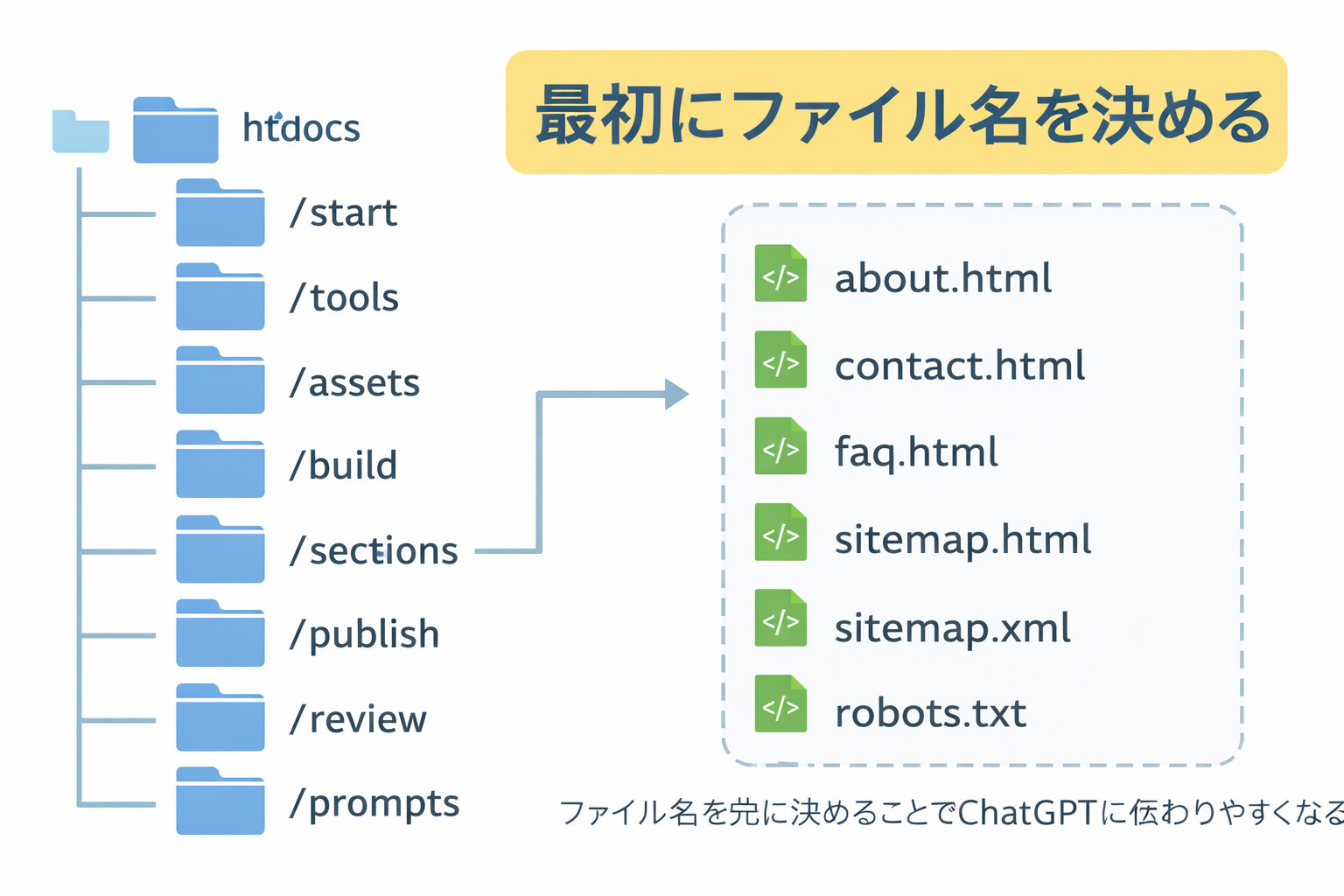
This site was built around the belief that practical control should be teachable. Not everyone needs to become an engineer. But far more people can learn enough to understand their files, organize their pages, manage their assets, and direct AI or contractors from a position of clarity rather than dependence.
That is why the training sequence here emphasizes local-first work, filename discipline, image control, reusable CSS and JavaScript, and structured review. These are not merely technical preferences. They are anti-hostage habits.
Files are power
One of the deepest truths in digital business is that file access is not a side detail. It is power. Whoever has the current version, the organized structure, the usable source, and the working credentials has leverage, whether they intend to or not.
That is why filenames matter. That is why asset libraries matter. That is why common CSS and JS matter. That is why image URLs matter. That is why backups matter. Structure is not bureaucracy. Structure is operational freedom.
A system is not truly yours just because your logo is on it.
Ownership without access, understanding, and replaceability is partial ownership at best.
How to reduce hostage risk
The answer is not paranoia. It is discipline.
A healthier business posture includes:
- clear access to domains, hosting, and accounts
- organized local copies of critical files
- consistent naming systems
- reusable shared assets and styles
- written structure rather than memory-only workflows
- the ability to hand the project to someone else if needed
The key question is not whether someone else can help. Of course they can. The key question is whether help increases your capability or replaces it with dependency.
A good partner leaves you stronger, not more helpless.
The best technical help creates clarity, continuity, and transferability.
Why AI changes the balance
AI is not a complete solution to hostage risk, but it changes the balance dramatically. It gives business owners and builders a practical way to ask questions, organize structures, generate files, revise code, explain workflows, and inspect outputs. It restores a layer of agency that had been missing for many people.
That does not mean AI eliminates the need for specialists. It means the owner can increasingly participate in the structure of their own systems instead of being locked outside them.

The deeper business principle
“Never let your business be held hostage” is bigger than websites. It means:
- do not let core knowledge exist only in one person’s head
- do not let ownership become vague
- do not let tools become mystical black boxes
- do not let urgency force blind dependence
- do not confuse activity with control
A calm business is not one with no complexity. It is one where complexity is organized, documented, and survivable.
Why this lesson belongs in the history section
Because it is not merely a tip. It is a worldview. It is one of the principles that explains why website.co.jp exists at all. This site is not trying to produce prettier pages alone. It is trying to teach a way of building that makes the business less fragile.
The historical significance is this: we are in a moment where AI can help reopen practical control. That matters most to the people who have already felt what technical captivity costs.

The final rule
You do not need to do every task personally forever. But you should design your business so that no single person, missing file, hidden process, or technical gate can freeze your ability to move.
That is not stubbornness. That is stewardship.
Build systems that you can inspect, explain, and continue.
That is how a business stays mobile, resilient, and hard to trap.